What is privacy and how can it be achieved in bitcoin and other digital currencies? To understand this question, you need at least to understand how bitcoin transactions work and understand the basics of cryptography. Distributed Lab cryptographer Bogdan Skryabin reveals this topic in an exclusive article. Illustrations prepared by Katerina Krashtapuk.
Definitions and terms
Let’s start with some basic definitions. We need to understand that privacy, and the ways to ensure it, is a very voluminous topic.
There are two main terms that go into the concept of privacy: anonymity and untraceability. Anonymity refers to the inability to identify a user online. Untraceability refers to the inability to associate network activities with users.
Privacy in bitcoin
In the case of bitcoin, it can be noted that the property of anonymity is present in it, but in practice it is very easy to lose. The untraceability property is also not fully achieved: by analyzing the transaction graph, it is possible to establish the involvement of some transactions with some anonymous wallets and, consequently, with specific users, if the anonymity of at least one address has been violated.
The simplest bitcoin wallet can provide only a minimal level of privacy. The user engages new addresses for each incoming payment and change. In this case, it is already more difficult for someone who analyzes the transaction graph to assert some non-obvious facts about the users of the currency and their financial flows. Nevertheless, this level of privacy is easy to breach. In normal bitcoin use, you trust your counterparties with your privacy. The party receiving the payment will know the history of the coin’s origin, and the party sending the payment will be able to see the future history of the coin’s transfer. In addition, a lot of metadata is usually disclosed that can also be accessed by third parties, such as the type of transaction (service, commodity), the type of wallet used, the location of users, and the like.
Let’s take a look at what transaction data makes sense to hide first to ensure the highest level of privacy. It is data about the origin of coins, which in turn refers to a property such as fungibility, or fungibility, which is very important for any money and value. At the level of the bitcoin protocol, this property is of course enforced (i.e., all coins are the same and processed according to the same rules), but at the application level fungibility is easily broken. For example, some merchants can analyze the provenance history of accepted coins and reject payments if they do not like it.
In addition, hiding the amount of the transfer, the sender’s address and the recipient’s address in the body of the transaction is very important. Hiding users’ network addresses is also important to achieve confidentiality, which is usually achieved with darknet protocols such as Freenet, TOR and I2P. But what are the mechanisms and tools for hiding histories, amounts, and addresses? Let’s understand in order.
The CoinJoin method
Let’s start with the simplest method of confusing the transaction graph, called CoinJoin. It is a method of creating a shared transaction to introduce ambiguity into the origin of the coins being sent. It involves forming a group of users to create one shared transaction in which multiple payments are made simultaneously, rather than having users create separate transactions.
This idea was first proposed by Gregory Maxwell back in 2013 on the popular BitcoinTalk forum. Since then, many different modifications of this methodology have been proposed and developed, which improved one or another property of payments. Now we will talk about how CoinJoin works in its pure form, and then we will look at some of its most interesting modifications.
How CoinJoin works
Let’s imagine that there is a group of users in which everyone wants to pay for an item at a particular online store.
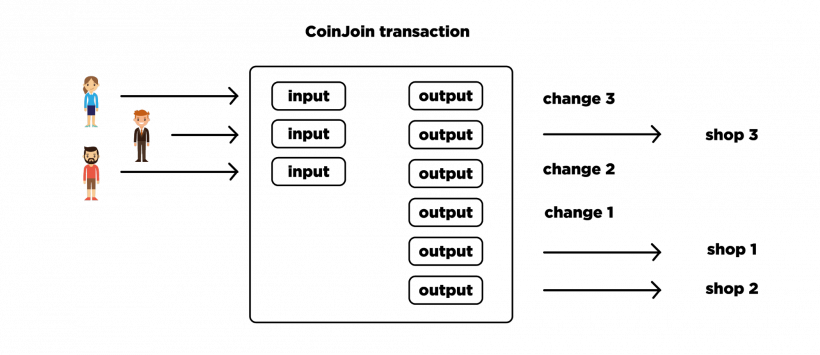
They make up one transaction where there are three inputs, one from each of them, three outputs, one for each online store, and three more outputs where each user picks up their change. Next, all of the exits are randomly shuffled among themselves. Each user double-checks the resulting transaction and signs the corresponding output. If successful, the transaction is considered correct, distributed to the network, and confirmed.
Regular Transactions VS. CoinJoin
In the following diagram you can see the difference between the graphs of regular transactions and CoinJoin transactions.
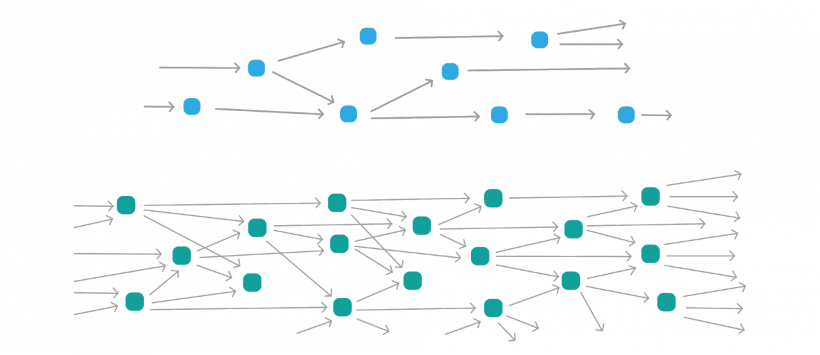
The top graph shows a graph where each transaction has one or two outputs, and the bottom graph shows a graph where transactions have three outputs each. The degree of entanglement in the lower graph is much higher and more difficult to analyze. In practice, wallets that use CoinJoin form groups of a large number of users. Then transactions can have dozens or even more inputs and outputs. If you depict the graph of such transactions on a plane, you get a lot of confusion. A coin that has gone through a chain of such transactions has thousands of possible origins. Searching among all variants the real one is difficult.
The Chaumian CoinJoin method
Now consider a modification of CoinJoin called Chaumian CoinJoin. It was proposed by the same Gregory Maxwell. The peculiarity of this modification is that it uses centralized operator and blind signature. The operator is needed to perform mixing of inputs and outputs, and then to compose the final transaction. However, the operator cannot steal coins or violate the confidentiality of the shuffle thanks to the blind signature. Blind signing works in such a way that the user pre-blinds the data during the shaping phase to transmit it to the operator. The operator, when signing this data, does not see the actual content. The signed data is returned to the user, then the user removes the blinding and everything looks like a normal electronic signature.
So how do users interact with the operator to form a common transaction? Each user prepares in advance the entrance where the coins belonging to him are spent, the address for receiving change, and the blinded address for sending the payment. The user combines this data into one sequence and passes it to the operator. The operator verifies the input and payment amounts, signs the output address, and returns the signature to the user. In doing so, the operator does not see the address to which the user wants to send the payment because the user is blinded. Next, the user removes the blinding from the output address, anonymously reconnects to the operator, and hands over the signed output address. The operator, in turn, verifies that he has indeed signed this address with his key and that he already has the corresponding input, but he cannot know which input corresponds to which output. Once all users have performed such actions, they reconnect anonymously to the operator again and provide signatures that confirm the ownership of the coins at the input of the overall transaction. The finished transaction can then be distributed to the network for confirmation.
In such a scheme, neither the users nor the operator itself can de-anonymize the coins at the output addresses. And the formation of a transaction under normal conditions takes no more than one minute. Interaction between users must be conducted via anonymous data networks, which can be TOR, I2P or Bitmessage.
Obviously, there may be unscrupulous participants among users, whose goal is to disrupt the process of creating a common transaction by any means. There is a whole list of possible scenarios of user behavior, including fraudulent ones. To counter adverse scenarios, a number of protection mechanisms have been developed to ensure that honest users are guaranteed to achieve the formation of the final transaction. The protection mechanisms use timeouts, tracking of unspent outputs, and the like. You can read more about all the scenarios and protection mechanisms separately. And now we will move on to the next modification of CoinJoin, which is called CoinShuffle.
CoinShuffle modification
The CoinShuffle modification was offered in 2014. Its advantage is that there is no central operator. Users form a common transaction on their own, communicating with each other. At the same time, they still cannot break the confidentiality of the mixing of the output addresses. Another advantage of this technique is that users do not need to use additional networks to anonymize traffic, as all the necessary properties will be achieved by using a single P2P protocol interaction between the participants.
This technique uses directional encryption, which involves a pair of keys (public and private). The message is encrypted with the public key, and only the owner of the private key can decrypt it. The DiceMix protocol is used for communication between the participants, and there is also provision for counteraction against intruders.
CoinShuffle principle of operation
Let’s understand schematically how CoinShuffle works in the simplest version.
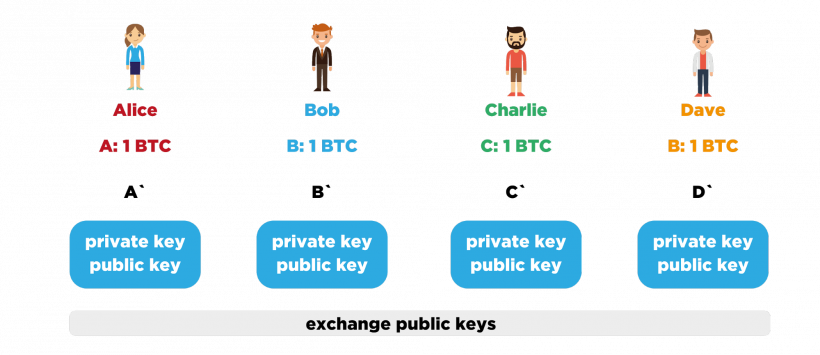
Let’s take a small group of users as an example: sly Alice, wise Bob, bearded Charlie, and orange Dave. Each of them has one unspent coin in the bitcoin blockchain at addresses A, B, C, and D, respectively. Each wants to spend the coin while hiding its origin story. To this end, each member of the group learns the address to which the A, B, C or D coin should be sent, respectively, but does not divulge that address to the other members. Next, each generates a new key pair for directional encryption, and then the group members exchange the keys open for encryption among themselves, with the new public key being signed by the private key that corresponds to the address with the unspent coin. In the same way all messages of the participants in the subsequent interaction will be signed. This was the first stage.
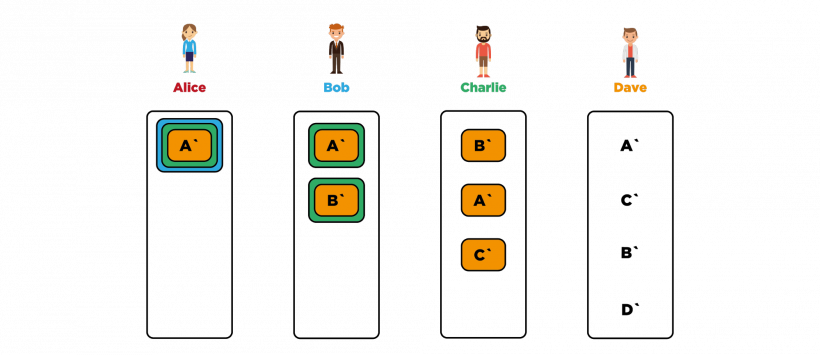
Next, the participants mix and form a line. Let Alice be first in our case because she is cunning, Bob second because he is wise, etc. Now Alice takes A’ and encrypts directed to Dave, using Dave’s public key accordingly. The resulting ciphertext Alice encrypts again, and directed to Charlie. This ciphertext is encrypted again, but directed to Bob. Alice gives the result of encryption to Bob. Bob decrypts the received message with his personal key. Then he takes B’ and encrypts it directed to Dave, then to Charlie and adds it to the list. He shuffles the list at random and hands it to Charlie. Charlie in turn decrypts the items on the list with his private key, adds C’, encrypted directly to Dave, to the list, and shuffles all the items on the list at random. The list is passed to Dave, who decrypts it, gets the public address data to send the coins, adds address D’, shuffles it randomly, and forms a total transaction based on those addresses, known transaction inputs, and sums.
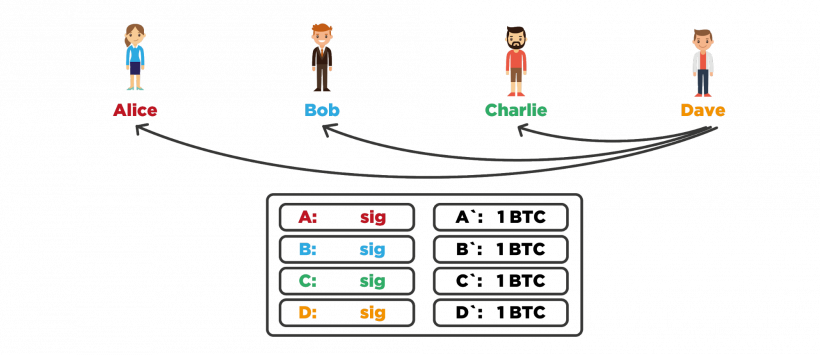
Dave distributes the transaction template to the rest of the group. Next, everyone checks closely to see if the output of the transaction has the address they want and if the amount matches. If all is well, the participant signs the transaction, confirming ownership of their entry’s coins. Participants exchange signatures and if the transaction gains all the necessary signatures, it can be distributed to the network for confirmation.
An important feature is that if one of the participants begins to deviate from the basic scenario of interaction, the others can jointly analyze the history of interaction and take the offenders out of the group to repeat everything without them.
It is worth noting that there are already ready implementations of CoinShuffle. And in practice, they work effectively even on groups of several dozens of users. Integration of this protocol into some bitcoin wallets, including mobile wallets, is expected at the moment.
Disadvantages of CoinJoin
Let’s look at the main disadvantages of the CoinJoin methodology. Obviously, there is a great complexity of off-chain interaction to form a transaction, i.e. it is necessary to organize the formation of groups and interaction of participants among themselves. But a more significant disadvantage is that CoinJoin in its pure form does not hide transfer amounts. As a result, it is vulnerable to CoinJoin Sudoku analysis, which is based on comparing amounts on transaction outputs and allows unraveling the coin origin story after repeatedly confusing it. Yes, this problem can be dealt with by, for example, using only certain amounts (0.1 VTS, 1 VTS, 10 VTS, etc.) for transaction outputs, but this creates additional complexity and limitations. So let’s consider a completely different method that solves the problem of open transfer amounts. It is called Confidential Transactions.
Confidential Transactions
The Confidential Transactions (CT) method has the peculiarity that it completely hides the actual amounts of transaction inputs and outputs from third parties. At the same time it allows everyone to check that the sum of all outputs does not exceed the sum of all inputs, which is already enough to validate the transaction. This is made possible through the use of zero-knowledge proof – it is a cryptographic proof of knowledge of some secret, but without disclosing the latter. To prove that the sum of outputs does not exceed the sum of inputs, Petersen Commitment is used, which is based on transformations in a group of points on an elliptic curve. In order to combat uncontrolled coin issuance, this scheme necessarily applies proof of the use of admissible amounts in the output of a transaction. To verify that non-negative amounts that do not exceed the order of a base point have been used, so-called Range Proofs are used.
And everything would be fine, but creating these very Range Proofs is very expensive in terms of computing resources. In addition, they have a very large volume. Theoretically, it is possible to integrate Confidential Transactions into the bitcoin protocol, but no one is in a particular hurry to do so because of their large volume. Nevertheless, there are already working accounting systems where Confidential Transactions are successfully used.
Ring Confidential Transactions
Consider the following technique, called Ring Confidential Transactions. It features the use of ring signatures to obfuscate the origin story of coins. It works so that the sender in the input of his transaction refers not to one particular output (UTXO), but to several, and uses a ring signature to prove that he owns coins from one of several outputs, but does not disclose which one. It follows that it is impossible to trace unequivocally the origin of the coins.
The use of ring signatures in this way was first proposed in the CryptoNote protocol, on which several cryptocurrencies operate. In addition, Ring Confidential Transactions use the CTs that we have already discussed. They allow you to create transactions with multiple inputs and outputs, where the origin of each input cannot be uniquely traced, transfer amounts are hidden, and no interaction with other users is required to create a transaction.
Stealth Addresses
Let’s take a look at Stealth Addresses and the benefits of using them. In essence, it is a technique of stealthy calculation of the addresses to which coins will be sent. This idea was first described by Peter Todd. It uses public keys as user IDs, i.e. if you want to accept payments you have to publicize your public key. Then the sender uses his key pair and your public key to compute a new one-time public key which will already be in the transaction as the address. It turns out that only the sender and the recipient can know the address to which the coins are sent. To an outside observer, the connection between the user ID and the address at the output of the transaction cannot be established, which also greatly increases the privacy of digital currency use.
Application in practice
Let’s now look at where the methods we talked about are applied.
Bitshares cryptocurrency was one of the first to implement CT in conjunction with Stealth Addresses, not only for the base currency, but also for tokens that can be issued on the platform. Monero cryptocurrency supports ring signatures and Stealth Addresses to ensure a high level of privacy. The team implemented RingCT in January 2017, and with an update in September 2017, the use of RingCT became strictly mandatory. Also of note is the Mimblewimble protocol, which uses a modified version of Confidential Transactions, which is now under active development, but we’ll talk about it later.
Let’s not overlook the ZeroLink project, which is a framework for creating confidential wallets based on the Chaumian CoinJoin methodology. Remarkably, it can work in bitcoin without requiring any changes to the protocol itself. We are done with the thematic part. Now let’s move on to the frequently asked questions on this topic.
Frequently Asked Questions on the Subject
Существует ли возможность использовать Stealth Addresses в биткоине?
Yes, you can use them now, you don’t need to update the protocol for that. But in order to adapt this functionality more widely, you need to strictly specify the order of calculations and data formats so that all wallets can work with each other, and add this feature to the wallets themselves accordingly. Peter Todd has already created a separate BIP to introduce this specification, but it’s still under consideration.
Эффективно ли использовать CoinJoin в чистом виде для биткоинов?
No, it is inefficient in its pure form, because such transactions lend themselves to simple analysis by transfer amounts. Alternatively, you could use the same amounts for all participants, while avoiding trusted mixers who could either steal coins or break confidentiality.
Можно ли применять рассмотренные выше методики для обеспечения конфиденциальности в таких цифровых валютах, как Ethereum, Ripple и Stellar?
No, Ethereum, Ripple and Stellar use a completely different transaction model and a different way of accounting for coins, which are not subject to such privacy techniques. You can, of course, try to artificially integrate some techniques like Stealth Addresses or Confidential Transactions, but that would be extremely inefficient in terms of currency performance. The reason is that Bitcoin keeps records based on unspent outputs (i.e. UTXO), and these currencies use accounts and balances.
Read more articles about cryptocurrencies and mining at COOL-MINING.ORG.
Do you like to read similar articles about cryptocurrencies and mining, do you want to support me as an author or ask questions? Be the first to know the news, subscribe to my telegram channel
Recommended articles on the topic:
Bitcoin exchange Poloniex denied data leak
Deutsche Bank analysts compared cryptocurrency development to Internet development
The TON community launched its own version of blockchain without Telegram
SWIFT has accelerated international payments, but it’s still far behind Ripple
Hackers’ ransomware virus DarkSide shuts down US fuel pipeline